Global Data Breach Notification: Your SMB's Guide to Timely Response
A data breach isn’t a matter of “if,” but “when.” For technology-driven businesses like SaaS startups, e-commerce platforms, digital agencies, and regulated service providers, the stakes are incredibly high. You’re handling sensitive information, and a breach can have far-reaching consequences, from reputational damage to significant financial penalties.
Beyond the immediate technical response, one of the most critical aspects of managing a breach is understanding and adhering to global data breach notification requirements. These aren’t one-size-fits-all rules; they vary significantly by region and even by state. For lean IT teams, staying on top of these can feel like a full-time job. Let’s break down what you need to know to ensure a timely and compliant response.
The GDPR Standard: A Swift 72-Hour Clock
If your business processes the personal data of individuals in the European Union (EU) or European Economic Area (EEA), the General Data Protection Regulation (GDPR) is your primary concern. GDPR is known for its strict and rapid notification timeline.

For GDPR-regulated businesses, the 72-hour clock starts ticking the moment you're aware of a breach.
Here’s the core of it:
- 72-Hour Notification to Authorities: You must notify the relevant Data Protection Authority (DPA) of a data breach within 72 hours of becoming aware of it. This isn’t 72 business hours; it’s 72 calendar hours. Even if you don’t have all the details, you should provide what you know and explain why information is missing.
- Notification to Data Subjects (If High Risk): If the breach is likely to result in a “high risk” to the rights and freedoms of individuals (e.g., identity theft, significant financial loss), you must also notify the affected data subjects directly, “without undue delay.” This typically means as soon as possible after you’ve assessed the risk.
The GDPR emphasizes accountability, meaning you need to be able to demonstrate your compliance, including the steps taken to address the breach and your rationale for any notification decisions.
Navigating the Patchwork: U.S. State Breach Notification Laws
The United States doesn’t have a single, overarching federal data breach notification law that covers all industries. Instead, it operates on a state-by-state basis, with each state having its own specific requirements. While the specifics differ, a common theme is the requirement for “prompt notice” or “without unreasonable delay.”
For example:
- California: Under the California Consumer Privacy Act (CCPA) and California’s breach notification law, businesses generally need to notify affected individuals “in the most expedient time possible and without unreasonable delay.” While not a hard 72-hour rule like GDPR, common practice and regulatory guidance often point towards notification within 30 to 45 days of discovery, though earlier is always better.
These state laws often specify who needs to be notified (residents of that state), what information must be included in the notice, and sometimes even the method of notification.
Beyond the EU and U.S.: Global Similarities

A global view of breach notification laws—your compliance radar must cover every jurisdiction you operate in.
While GDPR and U.S. state laws are prominent, many other Western countries have adopted similar principles of prompt breach notification.
- Canada: Under the Personal Information Protection and Electronic Documents Act (PIPEDA), organizations must report breaches involving a “real risk of significant harm” to the Privacy Commissioner of Canada and notify affected individuals as soon as feasible after determining the breach has occurred.
- United Kingdom: Post-Brexit, the UK GDPR largely mirrors the EU GDPR’s 72-hour rule for notifying the Information Commissioner’s Office (ICO) and, where applicable, affected individuals.
- Australia: The Notifiable Data Breaches (NDB) scheme requires organizations to notify individuals whose personal information is involved in an eligible data breach, and to notify the Australian Information Commissioner (OAIC), as soon as they are aware.
The common thread across these jurisdictions is the expectation of prompt reporting to authorities and, for higher-risk breaches, to affected individuals.
What to Include in a Breach Notification
Regardless of the specific law, most breach notifications require similar core information. Preparing templates in advance can save precious time during a crisis.
Typically, you’ll need to provide:
- Type of data involved: What categories of personal information were compromised (e.g., names, email addresses, financial details, health records)?
- When the breach occurred (and was discovered): The approximate date or period of the breach, and when your organization identified it.
- Mitigation steps taken: What actions have you taken or are you taking to contain the breach, assess its impact, and prevent future occurrences?
- Contact information: How can affected individuals get more information or assistance?
- Advice for individuals: Recommendations for affected individuals to protect themselves (e.g., changing passwords, monitoring credit reports).
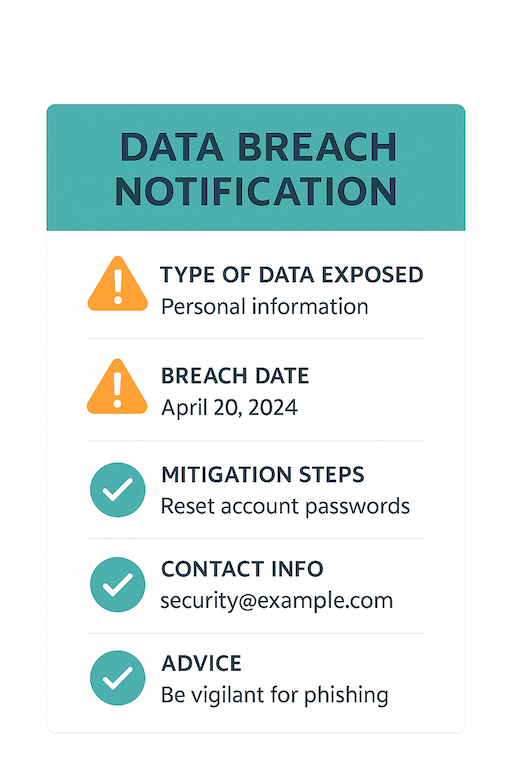
A well-structured notification ensures clarity, transparency, and compliance.
Preparing for the Inevitable: Practical Tips
Given the tight timelines and varied requirements, preparedness is key for any SMB.
- Develop an Incident Response Plan: This isn’t optional. A clear, documented plan outlines roles, responsibilities, and steps to take from detection to resolution and notification.
- Prepare Notification Templates: Draft generic notification letters for authorities and affected individuals. Having these ready to customize will drastically cut down on response time.
- Know Whom to Notify:
- Authorities: Identify the relevant DPAs or regulatory bodies based on your customer base and data processing activities.
- Customers/Individuals: Direct notification is often required for high-risk breaches.
- Credit Bureaus: For breaches involving sensitive financial information (e.g., Social Security numbers), you may need to notify major credit reporting agencies and offer credit monitoring services.
- Emphasize Incident Logging: Maintain a detailed log of every step taken during an incident. This includes discovery time, investigation steps, containment actions, communications, and decisions made. This log is crucial for demonstrating compliance and meeting deadlines, especially the GDPR’s 72-hour window.
Understanding and preparing for global data breach notification requirements is a critical component of your overall security posture. By having a plan, knowing the rules, and preparing your communications, you can navigate the complexities of a breach with greater confidence and minimize its impact.